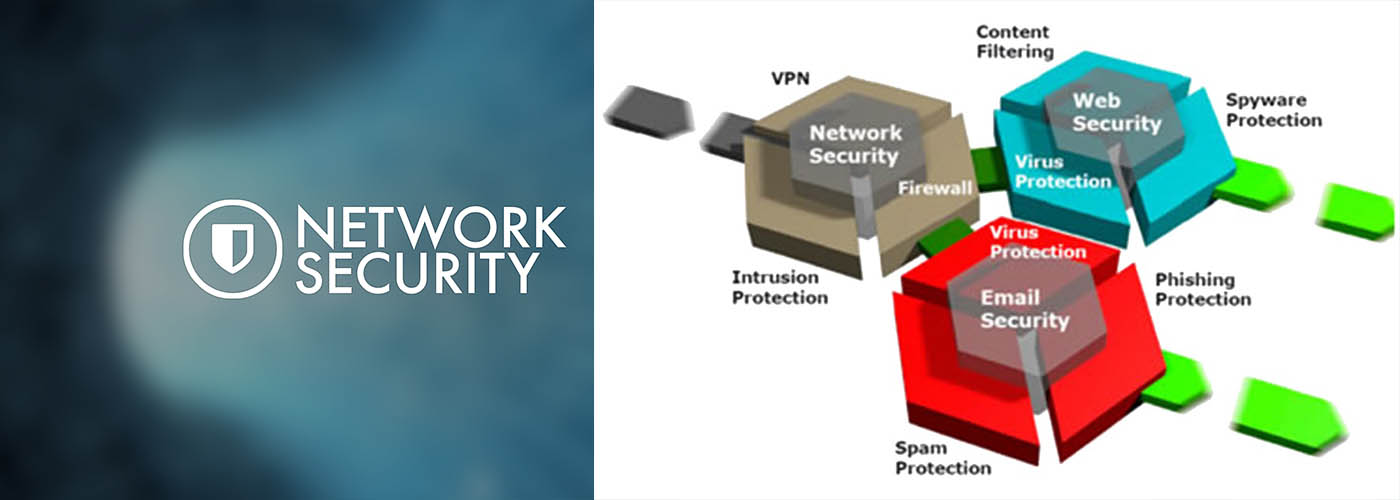
The moment your network connects to the internet, it becomes exposed to all types of viruses, malware and other threats circulating on the internet. Regardless of the size of your organization, it is important to ensure complete security of your network. Using network firewall is one of the primary ways of preventing your network from serious security threats.
Next Generation Firewalls (NGFWs) promise the best network security to the companies. Apart from having the capabilities of traditional firewalls such as packet filtering and network address translation (NAT), NGFWs offer intrusion prevention, deep-packet inspection and other useful features that traditional firewalls don’t have. Using next generation firewalls can go a long way when it comes to ensuring complete security for your network from all kinds of security threats.
We supply , install, and maintain Firewall that best protect against the latest advanced threats like ransomware, cryptomining, bots, worms, hacks, breaches and APTs.
- Powerful Sandstorm sandboxing
- Deep learning with artificial intelligence
- Top performing IPS
- Advanced threat and botnet protection
- Web protection with dual AV, JavaScript emulation and SSL inspection.